Keygraph
Unified AppSec: Static & Pentesting
Paid
Support platforms
web
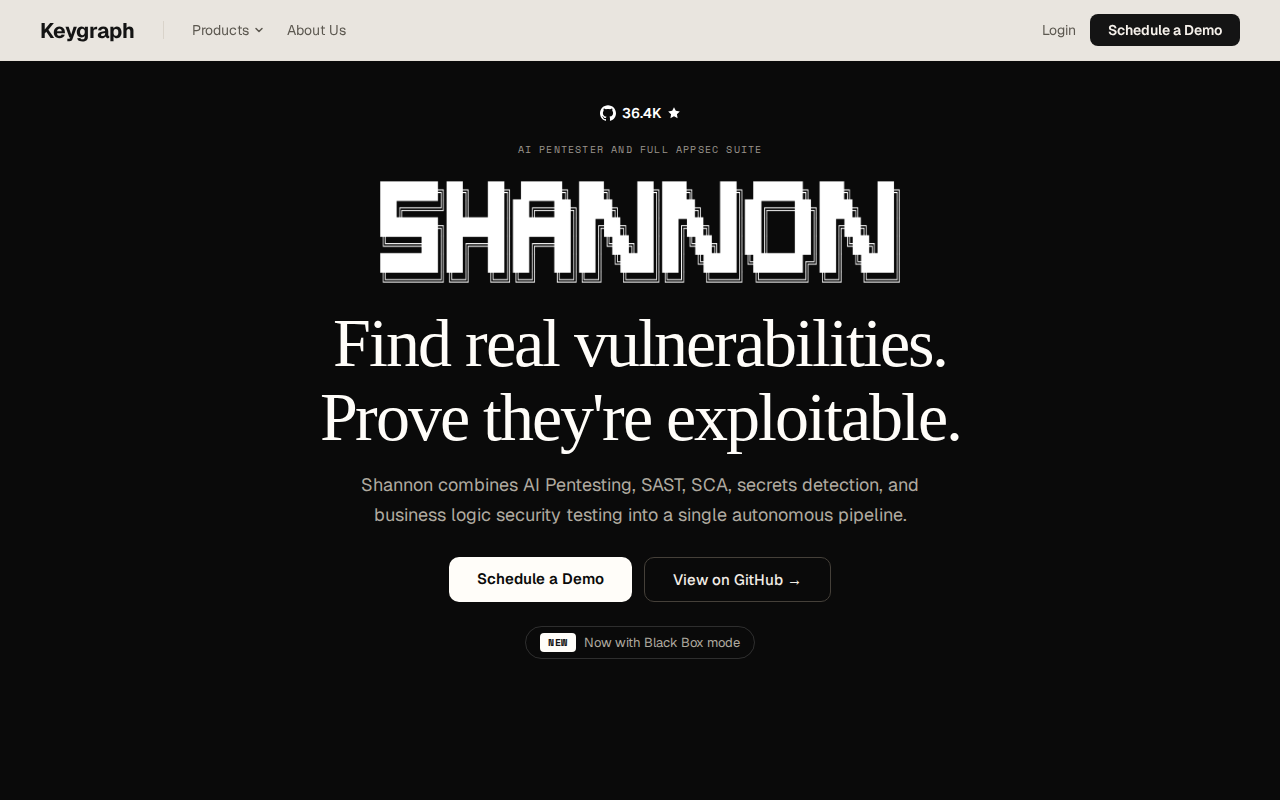
What is Keygraph
Keygraph is a unified application security (AppSec) platform designed to streamline vulnerability detection and validation. It combines agentic static analysis with autonomous penetration testing to identify real, exploitable vulnerabilities. Unlike traditional static analysis tools that often produce numerous false positives, Keygraph aims to provide actionable insights by proving the exploitability of identified issues. This platform differentiates itself through its agentic approach, which automates the process of vulnerability validation, reducing manual effort and improving accuracy. Keygraph is built for developers and security teams seeking to improve their application security posture efficiently. It helps them find and fix vulnerabilities faster, reducing the risk of security breaches and improving overall application security.
Keygraph 's Core features
Agentic Static Analysis
Keygraph employs agentic static analysis, which uses intelligent agents to analyze code. These agents automatically identify potential vulnerabilities and assess their exploitability. This approach reduces the number of false positives often associated with traditional static analysis tools, providing more accurate and actionable results. The agents simulate attacks to validate the vulnerabilities.
Autonomous Penetration Testing
The platform includes autonomous penetration testing capabilities. This feature automates the process of simulating attacks to validate identified vulnerabilities. By automating the testing process, Keygraph reduces the manual effort required to confirm the presence of vulnerabilities and provides developers with clear, actionable steps for remediation.
Unified Platform
Keygraph offers a unified platform that combines static analysis and penetration testing. This integration streamlines the vulnerability assessment process by providing a single interface for identifying, validating, and managing security issues. This unified approach reduces the need for multiple tools and simplifies the overall security workflow.
Exploitability Validation
Keygraph focuses on validating the exploitability of vulnerabilities. Unlike tools that simply identify potential issues, Keygraph attempts to prove that a vulnerability can be exploited. This validation process helps prioritize remediation efforts by focusing on the most critical and exploitable vulnerabilities, reducing the risk of actual security breaches.
Integration Capabilities
The platform is designed to integrate with existing development workflows. Keygraph can be integrated into CI/CD pipelines, allowing for automated security testing as part of the software development lifecycle. This integration ensures that security is addressed early and continuously, reducing the risk of vulnerabilities in production.
How to use Keygraph
- Visit the Keygraph website and explore the platform's features and capabilities. 2. Review the documentation to understand the platform's integration process. 3. Sign up for an account to access the platform. 4. Integrate Keygraph into your development workflow by connecting it to your codebase. 5. Run scans to identify potential vulnerabilities. 6. Review the results and prioritize remediation based on exploitability.
Use cases of Keygraph
Secure Code Development
Developers can use Keygraph to identify and fix vulnerabilities in their code during the development phase. By integrating the platform into their CI/CD pipeline, they can ensure that security is addressed early and continuously, preventing vulnerabilities from reaching production and reducing the risk of security breaches.
Vulnerability Prioritization
Security teams can use Keygraph to prioritize vulnerability remediation efforts. The platform's ability to validate the exploitability of vulnerabilities allows teams to focus on the most critical issues first. This approach ensures that resources are allocated efficiently, reducing the overall risk of security breaches.
Automated Security Testing
Security engineers can automate security testing processes using Keygraph. The platform's autonomous penetration testing capabilities automate the process of simulating attacks to validate identified vulnerabilities. This automation reduces the manual effort required to confirm the presence of vulnerabilities.
Compliance and Auditing
Organizations can use Keygraph to demonstrate compliance with security standards and regulations. The platform provides detailed reports on identified vulnerabilities and their exploitability, which can be used to support security audits and demonstrate a commitment to secure development practices.
Who benefits from Keygraph
Software Developers
Developers benefit from Keygraph by integrating it into their development workflow to identify and fix vulnerabilities early in the development lifecycle. This helps them write more secure code and reduce the risk of security breaches in their applications.
Security Engineers
Security engineers can use Keygraph to automate security testing processes and prioritize vulnerability remediation efforts. The platform's ability to validate the exploitability of vulnerabilities allows them to focus on the most critical issues first, improving overall security posture.
DevOps Teams
DevOps teams can integrate Keygraph into their CI/CD pipelines to automate security testing as part of the software development lifecycle. This ensures that security is addressed continuously, reducing the risk of vulnerabilities in production environments and streamlining the development process.
Pricing of Keygraph
Pricing not explicitly stated on the landing page. Requires contacting the vendor for details.