Apktool
Android APK Reverse Engineer
Free
Support platforms
web
What is Apktool
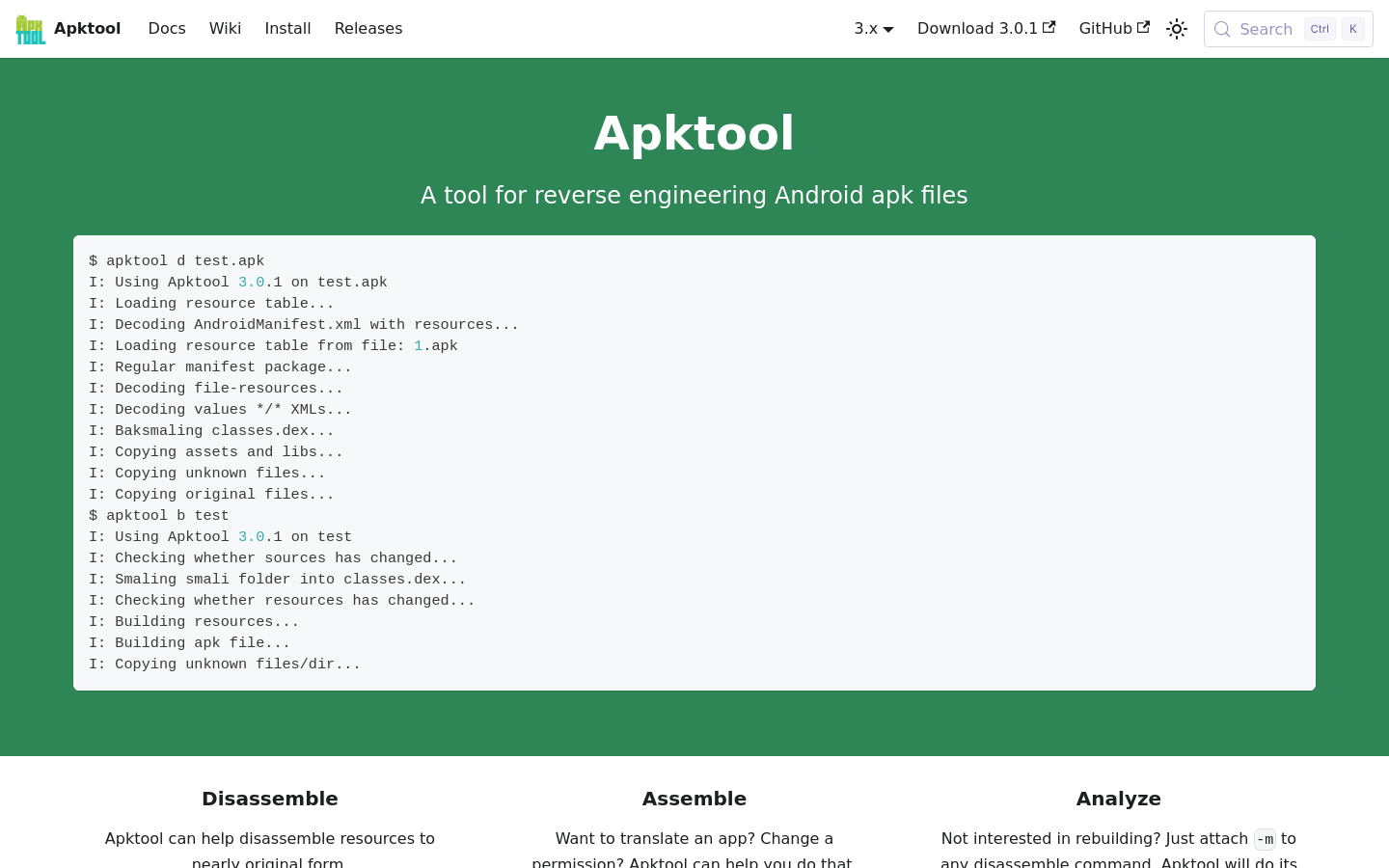
Apktool is the industry-standard command-line utility for reverse engineering third-party, closed-source Android applications. It enables developers and security researchers to decode resources to their nearly original form, modify them, and rebuild the APK. Unlike simple decompressors, Apktool handles the complex task of decoding AndroidManifest.xml, resources.arsc, and smali files, allowing for deep inspection of app logic and asset structures. It is essential for security auditing, localization, and debugging proprietary binaries where source code is unavailable.
Apktool 's Core features
Resource Decoding and Rebuilding
Apktool decodes the binary 'resources.arsc' file and XML layouts into human-readable formats. It correctly handles the complex Android resource ID mapping, ensuring that when you rebuild the APK, the resource references remain intact. This is critical for translating apps or modifying UI elements without breaking the application's internal resource lookup table.
Smali Code Disassembly
It disassembles the 'classes.dex' bytecode into Smali, an assembly-like language for the Dalvik VM. This allows developers to analyze the exact logic flow of an application. By converting bytecode to Smali, users can perform fine-grained edits to app behavior, such as bypassing license checks or injecting logging, before reassembling the code back into functional DEX files.
Manifest Analysis and Modification
The tool automatically decodes the 'AndroidManifest.xml' file, which is typically stored in a binary format. By making this file human-readable, Apktool allows security researchers to inspect requested permissions, exported components, and intent filters. This is vital for identifying potential security vulnerabilities or privacy leaks within an application's configuration.
Framework Dependency Management
Android apps often rely on system-level resources. Apktool allows users to install framework files (like 'framework-res.apk') to provide the necessary context for decoding apps that use custom system themes or proprietary manufacturer APIs. This ensures that resource decoding does not fail due to missing references to standard Android system components.
Cross-Platform CLI Interface
Built as a Java-based command-line tool, Apktool is platform-agnostic, running seamlessly on Windows, macOS, and Linux. Its CLI-first design makes it highly scriptable, allowing security teams to integrate APK analysis into automated CI/CD pipelines or batch processing scripts for large-scale vulnerability scanning across thousands of APK files.
How to use Apktool
- Install the Java Runtime Environment (JRE) 1.8 or higher on your system.,2. Download the latest 'apktool.jar' file from the official GitHub releases page.,3. Run 'java -jar apktool.jar d app.apk' to disassemble the target APK into a readable directory structure.,4. Modify the desired smali files, resource XMLs, or manifest permissions within the output folder.,5. Execute 'java -jar apktool.jar b folder_name -o modified_app.apk' to reassemble the application.,6. Sign the newly generated APK using 'apksigner' before attempting to install it on an Android device.
Use cases of Apktool
Security Auditing
Security researchers use Apktool to decompile apps to identify hardcoded API keys, insecure storage practices, or malicious code patterns. By inspecting the Smali and manifest files, they can verify if an app adheres to security best practices before deployment.
App Localization
Developers or translators use Apktool to extract string resources from closed-source apps. By modifying the 'strings.xml' files and rebuilding the APK, they can add support for new languages without needing access to the original source code repository.
Modding and Customization
Power users and modders use Apktool to customize app behavior, such as removing ads, changing UI themes, or enabling hidden features. By disassembling the app, they can patch Smali logic to alter how the application interacts with the user.
Who benefits from Apktool
Security Researchers
They require deep visibility into binary code to perform penetration testing, vulnerability assessment, and malware analysis on Android applications where source code is unavailable.
Android Developers
They use the tool to debug issues in their own apps when source code is lost or to inspect how third-party libraries are implemented within their project.
Localization Specialists
They need to extract and re-inject localized strings into compiled APKs to provide language support for apps that lack official internationalization features.
Pricing of Apktool
Open source project distributed under the Apache License 2.0. Completely free to use, modify, and distribute.