IronClaw: Unleash Your AI Agent, With Peace of Mind
TEE-secured AI agent runtime
Free
Support platforms
web

What is IronClaw: Unleash Your AI Agent, With Peace of Mind
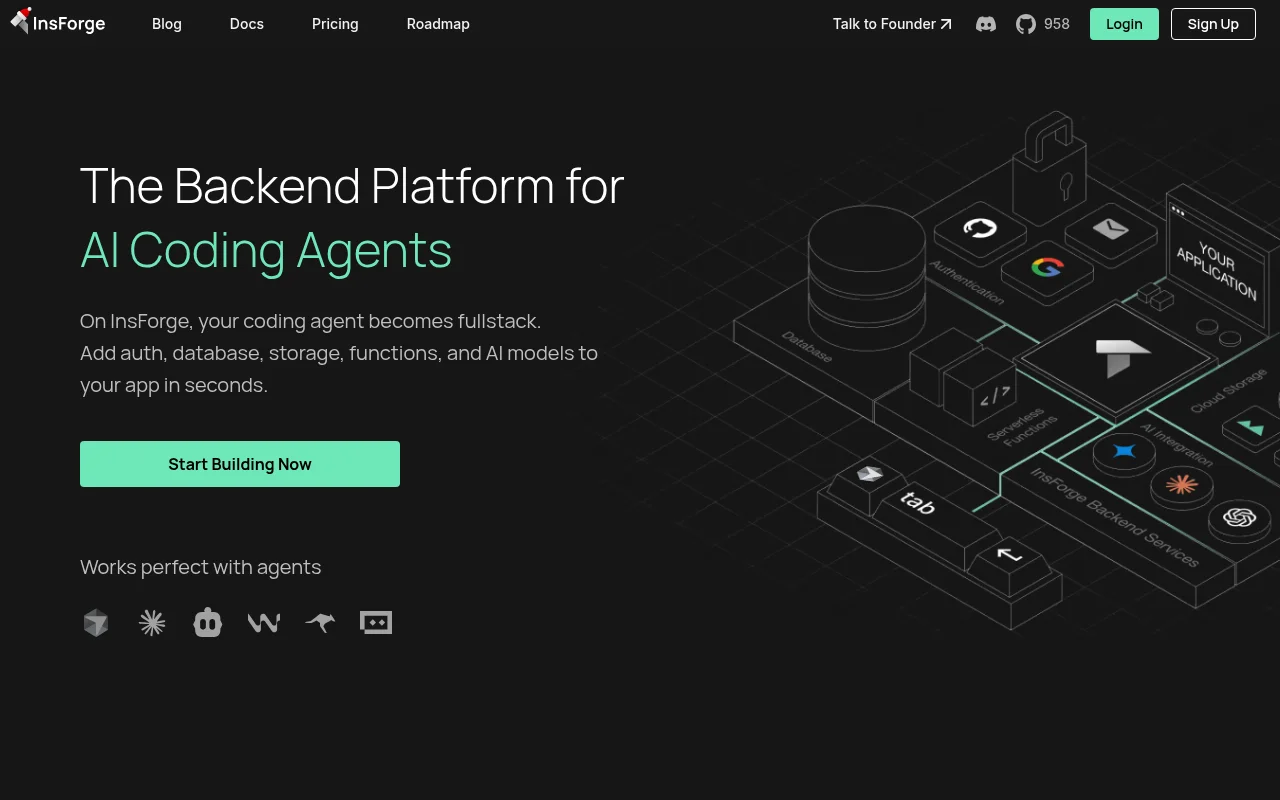
IronClaw is an open-source, security-first runtime for AI agents, designed as a hardened alternative to OpenClaw. It addresses the critical vulnerability of credential exposure by executing agents within Trusted Execution Environments (TEEs) on the NEAR AI Cloud. Unlike standard agent frameworks where LLMs have direct access to raw API keys, IronClaw uses an encrypted vault that injects credentials only into authorized, allow-listed network requests. By leveraging Rust for memory safety and TEE-based isolation, it mitigates risks like prompt injection and unauthorized data exfiltration. It is ideal for developers building autonomous agents that require access to sensitive production APIs, financial services, or private user data.
IronClaw: Unleash Your AI Agent, With Peace of Mind 's Core features
Trusted Execution Environment (TEE)
IronClaw runs agents inside hardware-encrypted enclaves. This ensures that even if the underlying host OS or hypervisor is compromised, the agent's memory and internal state remain encrypted and inaccessible to external processes. This provides a defense-in-depth layer that standard containerized environments cannot match, effectively isolating the agent's execution from the cloud provider's infrastructure.
Credential Vaulting & Injection
Instead of passing raw keys to the LLM, IronClaw stores secrets in a hardened vault. The runtime acts as a secure proxy, injecting credentials into outgoing HTTP requests only when the destination URL matches a pre-configured allow-list. This prevents prompt injection attacks from exfiltrating keys, as the LLM never sees the raw secret values, only the result of the authorized request.
Memory-Safe Rust Architecture
The core runtime is built in Rust, leveraging its strict ownership model and borrow checker to eliminate common memory corruption vulnerabilities like buffer overflows or use-after-free errors. By ensuring memory safety at the language level, IronClaw reduces the attack surface for exploits that target the agent's runtime environment, providing a robust foundation for high-stakes automation.
Granular Network Allow-listing
IronClaw enforces strict egress filtering via an AllowList struct. By explicitly defining which endpoints an agent can communicate with, developers prevent unauthorized data exfiltration to malicious servers. The runtime validates every request against this list before applying authentication headers, ensuring that even a compromised agent cannot send sensitive data to an unapproved third-party domain.
WASM-based Security Validation
The platform utilizes `wasmparser` to validate agent code before execution. By scanning for unsafe operations and ensuring the bytecode conforms to strict safety standards, IronClaw prevents the execution of malicious or malformed agent logic. This automated verification step occurs during deployment, ensuring that only audited and safe code is permitted to run within the TEE.
How to use IronClaw: Unleash Your AI Agent, With Peace of Mind
- Clone the IronClaw repository from GitHub and review the source code for security auditing.,2. Configure your agent's environment by defining an 'AllowList' of permitted API endpoints in the config file.,3. Provision a TEE instance on the NEAR AI Cloud using the IronClaw CLI deployment command.,4. Populate the encrypted vault with your sensitive API keys, bearer tokens, and authentication secrets.,5. Launch the agent process, which initializes the TEE and binds the vault to the restricted network allow-list.,6. Monitor agent activity through the secure enclave logs to ensure all outbound traffic adheres to your defined security policies.
Use cases of IronClaw: Unleash Your AI Agent, With Peace of Mind
Financial Transaction Automation
Developers building agents to manage crypto wallets or bank APIs use IronClaw to ensure that API keys are never exposed to the LLM's context window, preventing unauthorized fund transfers via prompt injection.
Enterprise Data Retrieval
Corporate AI agents accessing internal databases or private SaaS tools use IronClaw to restrict data access to specific, pre-approved endpoints, ensuring compliance with internal security and data privacy policies.
Secure Third-Party API Integration
Engineers deploying agents that interact with multiple third-party services (e.g., GitHub, Jira, Slack) use IronClaw to manage disparate credentials in a single, isolated vault, minimizing the risk of credential leakage.
Who benefits from IronClaw: Unleash Your AI Agent, With Peace of Mind
AI Security Engineers
They need to deploy autonomous agents in production environments without exposing sensitive credentials to LLM providers or potential prompt injection attacks.
FinTech Developers
They require high-assurance execution environments for agents handling sensitive financial data, where memory safety and hardware-level isolation are regulatory requirements.
Open Source Contributors
They seek a transparent, auditable, and secure framework for building and deploying AI agents that prioritize user privacy and data sovereignty.
Pricing of IronClaw: Unleash Your AI Agent, With Peace of Mind
Open-source software. The runtime is free to use; infrastructure costs are determined by the NEAR AI Cloud deployment model.