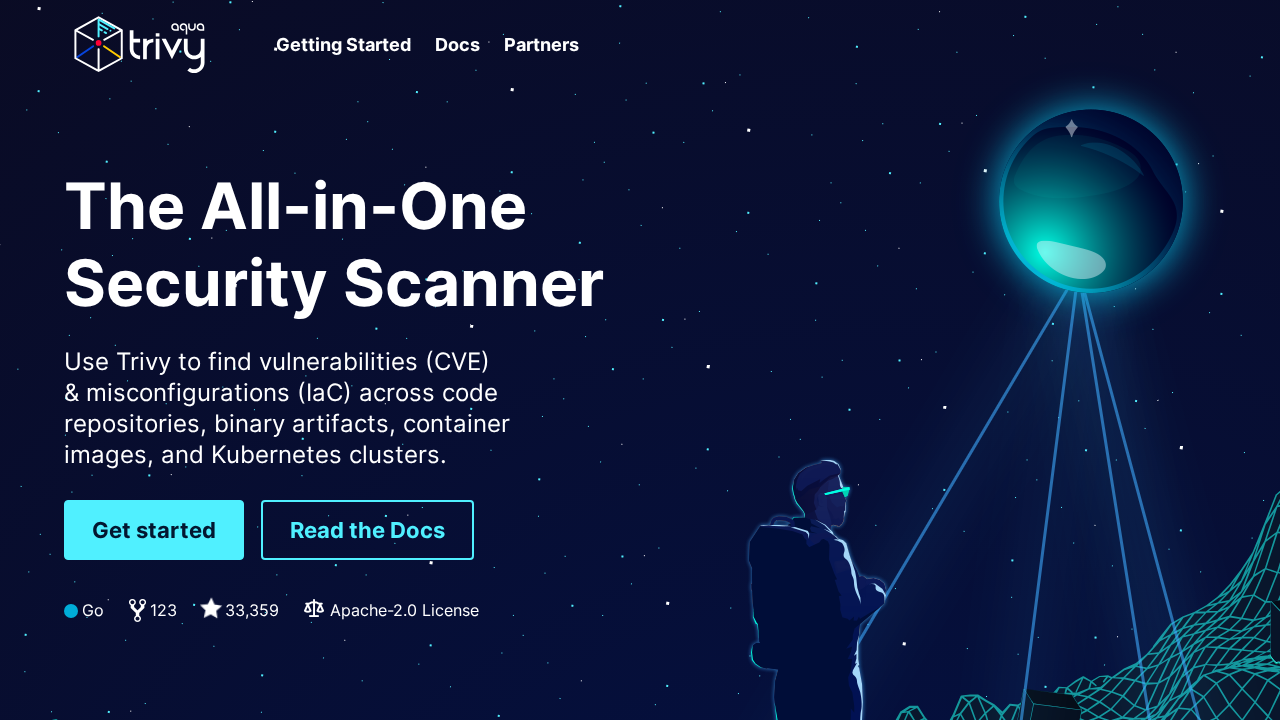
Trivy
Open-source security scanner
Free
Support platforms
web
What is Trivy
Trivy is a comprehensive, open-source security scanner designed to identify vulnerabilities and misconfigurations in container images, code repositories, infrastructure as code (IaC), and Kubernetes clusters. Its core value lies in providing a unified solution for security scanning across the entire software development lifecycle, from build to deployment. Unlike many commercial alternatives, Trivy's open-source nature fosters community contributions and transparency. It leverages a vulnerability database and supports various formats, including SBOMs. Trivy's architecture focuses on ease of use and performance, making it suitable for developers, DevOps engineers, and security professionals. It simplifies security audits and helps organizations proactively address security risks, improving their overall security posture.
Trivy 's Core features
Vulnerability Scanning
Trivy scans container images, file systems, and IaC configurations for known vulnerabilities (CVEs). It leverages a continuously updated vulnerability database, ensuring accurate and up-to-date results. The scanner supports various package managers and programming languages, providing broad coverage. Results are displayed with severity levels (Critical, High, Medium, Low) and include details such as affected packages and suggested remediation steps.
IaC Configuration Scanning
Trivy identifies misconfigurations in Infrastructure as Code (IaC) files, such as Terraform, CloudFormation, and Kubernetes manifests. It checks for security best practices and potential vulnerabilities in your infrastructure setup. This helps prevent security breaches caused by misconfigured resources. The tool supports a wide range of configuration file formats and provides detailed reports on identified issues, including severity levels and remediation guidance.
SBOM Generation
Trivy generates Software Bill of Materials (SBOMs) in various formats (e.g., SPDX, CycloneDX) for container images and file systems. This provides a comprehensive inventory of all software components and their dependencies. This is crucial for supply chain security, vulnerability management, and compliance. The SBOMs can be used to track and manage software components, identify vulnerabilities, and ensure compliance with security policies.
Kubernetes Security Scanning
Trivy scans Kubernetes clusters for security vulnerabilities and misconfigurations. It analyzes Kubernetes resources (e.g., deployments, pods, services) against security best practices. It identifies potential issues related to security contexts, network policies, and resource limits. The tool provides detailed reports with recommendations to improve the security posture of your Kubernetes deployments, helping to prevent unauthorized access and data breaches.
Multi-Platform Support
Trivy supports scanning across multiple platforms, including Linux, Windows, and macOS. It can scan container images from various registries (Docker Hub, private registries), local file systems, and IaC configurations. This cross-platform compatibility ensures that security scanning can be integrated into diverse development and deployment environments. The tool's flexibility makes it suitable for organizations with heterogeneous infrastructure.
Ease of Use
Trivy is designed for ease of use, with a simple command-line interface and clear output. It requires minimal configuration and can be integrated into CI/CD pipelines with ease. The tool's straightforward design allows developers and security professionals to quickly scan their projects and identify vulnerabilities. The intuitive interface and detailed documentation make it accessible to users of all skill levels.
How to use Trivy
- Download the Trivy binary for your operating system from the releases page on GitHub (https://github.com/aquasecurity/trivy/releases).,2. Install the binary by moving it to a directory in your system's PATH (e.g., /usr/local/bin).,3. Scan a container image: Run
trivy image <image_name>:<tag>(e.g.,trivy image nginx:latest).,4. Scan a local filesystem: Runtrivy fs <path_to_directory>(e.g.,trivy fs .).,5. Scan IaC files: Runtrivy config --severity HIGH <path_to_iac_file>(e.g.,trivy config --severity HIGH terraform.tf).,6. View the scan results in your terminal, which will list vulnerabilities, their severity, and potential fixes.
Use cases of Trivy
Container Image Scanning
A DevOps engineer uses Trivy to scan a newly built container image before deploying it to production. Trivy identifies several critical vulnerabilities in the image's base OS and installed packages. The engineer then rebuilds the image with updated dependencies, resolving the vulnerabilities and preventing potential security breaches in the deployed application.
IaC Configuration Auditing
A security engineer uses Trivy to scan Terraform configuration files for a new cloud infrastructure deployment. Trivy detects misconfigurations related to network security groups and IAM roles. The engineer corrects these configurations, ensuring that the infrastructure is deployed securely and compliant with organizational security policies, reducing the risk of unauthorized access.
Kubernetes Security Assessment
A Kubernetes administrator uses Trivy to scan a production Kubernetes cluster. Trivy identifies several security vulnerabilities in the cluster's configuration, such as insecure pod security policies and missing resource limits. The administrator then remediates these issues, strengthening the cluster's security posture and reducing the risk of a successful attack.
SBOM Generation for Compliance
A software development team uses Trivy to generate SBOMs for their containerized applications. This is done to comply with industry regulations and internal security policies. The SBOMs are then shared with the security team and used to track the software components and their dependencies, enabling proactive vulnerability management and supply chain security.
Who benefits from Trivy
DevOps Engineers
DevOps engineers need Trivy to integrate security scanning into their CI/CD pipelines. It helps them automate vulnerability detection in container images and IaC configurations, ensuring secure deployments and reducing the risk of security incidents. This allows them to shift security left and improve the overall security posture of their applications.
Security Professionals
Security professionals use Trivy to perform vulnerability assessments and security audits. They can use it to identify vulnerabilities in container images, Kubernetes clusters, and IaC configurations. This helps them proactively identify and mitigate security risks, ensuring compliance with security policies and industry best practices.
Software Developers
Software developers use Trivy to scan their code repositories and container images for vulnerabilities during the development process. This allows them to identify and fix security issues early in the development lifecycle, reducing the risk of deploying vulnerable code to production and improving the overall quality of their software.
Security Auditors
Security auditors use Trivy to assess the security posture of containerized applications and infrastructure. They can leverage Trivy's comprehensive scanning capabilities to identify vulnerabilities, misconfigurations, and compliance issues. This helps them provide accurate and detailed security reports, ensuring that organizations meet security standards and regulations.
Pricing of Trivy
Open source, available under the Apache-2.0 License. Free to use, with no paid plans or tiers.